Resource Monitors Used in Breaches: Key Tools for Early Detection and Cybersecurity Defense
How Resource Monitoring Tools Help Identify and Mitigate Security Threats in Real-Time
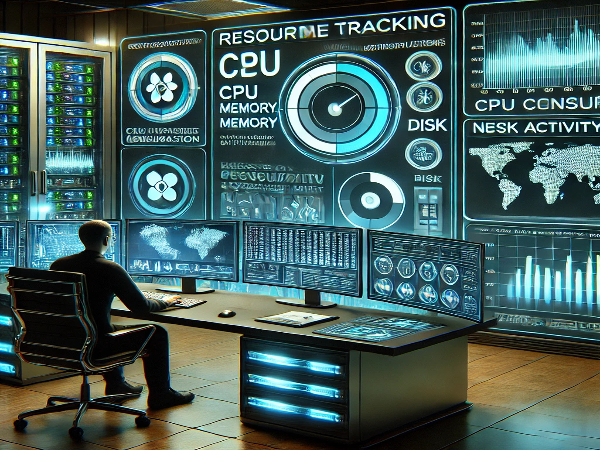
Resource monitors are essential tools in modern cybersecurity, offering real-time system performance and activity insights. These tools track key resources like CPU, memory, disk, and network usage, helping security teams identify unusual behavior that could indicate a potential breach. By monitoring for abnormal resource consumption, resource monitors can detect early signs of malicious activities, such as malware infections or unauthorized access. Their ability to flag irregularities allows cybersecurity teams to respond quickly, preventing or mitigating damage caused by cyber threats. As cyberattacks grow more sophisticated, leveraging resource monitoring tools has become an invaluable strategy for safeguarding organizational assets.
Introduction
In the ever-evolving landscape of cybersecurity, businesses and organizations are continuously under threat from malicious actors. With increasing amounts of sensitive data and systems vulnerable to breaches, it has become critical to employ proactive monitoring strategies to detect and mitigate these threats. One of the most effective methods for identifying breaches is through the use of resource monitors. These tools offer real-time insights into system performance, enabling security teams to detect anomalies that could indicate malicious activity. This article explores the importance of resource monitors in breach detection, their functionality, and their role in strengthening overall cybersecurity defense.
What Are Resource Monitors?
Resource monitors are tools used to track and analyze the performance of a system or network in real-time. They measure various metrics, including CPU usage, memory consumption, disk activity, and network traffic. By continuously monitoring these parameters, resource monitors can identify unusual spikes or patterns that could signify an ongoing breach or potential security threat. For example, a sudden surge in CPU usage or an unexpected increase in network traffic could indicate the presence of malware or a denial-of-service (DoS) attack.
Resource monitors are often integrated into larger cybersecurity frameworks, offering security teams a comprehensive view of system activity. These tools provide alerts or notifications when abnormal behavior is detected, enabling immediate intervention to prevent further damage. They can also be configured to automatically take corrective actions, such as isolating affected systems or blocking suspicious network traffic.
The Role of Resource Monitors in Detecting Cybersecurity Breaches
Resource monitors play a critical role in detecting cybersecurity breaches by highlighting abnormal system behaviors that may go unnoticed otherwise. Cybercriminals often attempt to disguise their malicious actions by making them appear as legitimate system activities. This can include manipulating system resources to avoid detection, such as consuming excessive CPU power or using up network bandwidth.
By continuously tracking resource usage, these tools can identify such hidden threats early on. They help cybersecurity teams identify when resources are being misused, allowing for swift action to isolate the threat before it causes widespread damage. Moreover, resource monitors can provide valuable data for forensic analysis, helping teams trace the origins and methods of the attack.
Key Metrics Tracked by Resource Monitors
Effective resource monitoring requires tracking various system metrics that reflect the health and performance of devices and networks. Some of the key metrics monitored by resource tools include:
CPU Usage:
The central processing unit (CPU) is the core of any system, and its usage directly affects the overall performance. A sudden spike in CPU usage could indicate that malware or other malicious software is running in the background, using excessive processing power. Monitoring CPU usage helps identify abnormal patterns and prevent overloading the system.
Memory Usage:
Memory (RAM) is a limited resource that is critical for system performance. Malicious software may try to consume more memory than necessary, leading to slower system responses or even system crashes. By monitoring memory usage, resource monitors can alert security teams to potential breaches before they cause significant disruptions.
Disk Activity:
Disk activity refers to the reading and writing processes that occur on a system’s hard drive. Unusual disk activity, such as high-frequency data writes or large amounts of data being transferred, could indicate unauthorized access or data exfiltration attempts. Resource monitors can track disk activity to prevent potential breaches from escalating.
Network Traffic:
Network traffic monitoring helps detect unusual patterns, such as unauthorized connections or large data transfers. Abnormal network traffic could be a sign of a breach, as hackers may try to communicate with external servers or exfiltrate sensitive data. Monitoring network usage enables early identification of such suspicious activities.
How Resource Monitors Identify Breaches
The key strength of resource monitors lies in their ability to detect abnormal behavior by comparing real-time system activity to predefined baselines or typical patterns. These tools use algorithms and threshold settings to establish what is “normal” behavior for each system component.
When a deviation from this baseline occurs, the resource monitor flags it as an anomaly. For example, if a system suddenly consumes an unusually high amount of memory or if network traffic exceeds normal levels, the tool can immediately generate an alert. This early warning allows cybersecurity teams to investigate further and determine whether the anomaly is a sign of a larger breach.
Advanced resource monitors can also integrate with other security tools, such as intrusion detection systems (IDS) or security information and event management (SIEM) platforms. This integration enhances their effectiveness by allowing for a more comprehensive approach to threat detection and response.
Benefits of Using Resource Monitors in Cybersecurity
Early Detection of Threats:
One of the primary benefits of resource monitors is their ability to detect threats early. By identifying unusual resource usage patterns, these tools can alert security teams before a breach becomes more serious. This proactive approach helps mitigate the impact of potential cyberattacks.
Improved Incident Response:
Resource monitors can help streamline incident response efforts. By providing real-time alerts and detailed system activity logs, they enable security teams to quickly assess the situation, identify the scope of the attack, and take appropriate action. This can include isolating affected systems, blocking malicious processes, or even shutting down compromised devices.
Reduced System Downtime:
By detecting breaches early, resource monitors can help reduce system downtime. Instead of waiting for an attack to fully unfold, security teams can intervene quickly to minimize disruptions and keep business operations running smoothly. This is particularly important in industries where uptime is critical, such as healthcare or finance.
Enhanced Security Posture:
Using resource monitors as part of a broader cybersecurity strategy helps organizations maintain a strong security posture. These tools provide valuable insights into system behavior, allowing organizations to spot vulnerabilities and weaknesses before they are exploited. Regular monitoring also helps identify potential compliance issues, ensuring that security policies are being followed.
Challenges in Using Resource Monitors
While resource monitors offer significant benefits, there are challenges that organizations must overcome to fully leverage these tools. One of the main challenges is the volume of data generated by continuous monitoring. Managing and analyzing large amounts of data can be time-consuming, and organizations may need advanced tools or trained personnel to handle the influx of information.
Additionally, resource monitors are only effective if they are properly configured. Incorrect thresholds or baselines can result in false positives or missed threats. Organizations must ensure that their monitoring tools are calibrated correctly to provide accurate alerts without overwhelming security teams with irrelevant notifications.
Best Practices for Implementing Resource Monitors
To maximize the effectiveness of resource monitors, organizations should follow these best practices:
Set Realistic Baselines:
Establish realistic performance baselines based on historical data to accurately detect deviations. These baselines should be adjusted regularly to account for changes in system behavior or usage patterns.
Integrate with Other Security Tools:
Combine resource monitors with other cybersecurity solutions, such as firewalls, intrusion detection systems, and SIEM platforms, for a more comprehensive defense against breaches.
Regularly Review Alerts:
Ensure that alerts generated by resource monitors are regularly reviewed by security teams to ensure timely action. False positives should be minimized by adjusting thresholds and fine-tuning settings.
Automate Response Actions:
Implement automated responses for common threats, such as isolating affected systems or blocking malicious IP addresses, to speed up the response time and prevent further damage.
Conclusion
Resource monitors are indispensable tools in the fight against cyber threats, offering real-time insights into system performance and identifying abnormal behaviors that may signal a breach. By tracking key metrics such as CPU, memory, disk, and network usage, these tools provide early detection capabilities, allowing cybersecurity teams to respond quickly and effectively. As cyberattacks become more sophisticated, resource monitors will continue to play a crucial role in safeguarding organizational assets, improving incident response, and enhancing overall cybersecurity defenses.
Incorporating resource monitoring as part of a broader cybersecurity strategy is essential for organizations looking to stay ahead of potential threats and mitigate the risks of data breaches. With the right tools and configurations in place, businesses can protect their systems, data, and reputation from the growing wave of cyberattacks.